Network Management
Grandstream's GWN series of Networking Solutions offer powerful and secure networks with wide coverage range that feature industry-leading setup and GDMS Networking and GWN Manager are free enterprise-grade, management platforms for Grandstream access points, routers, and switches. Thanks to streamlined monitoring and maintenance, managing your network or several networks across multiple locations has never been easier.
GDMS Networking
GDMS Networking is an enterprise-grade, management platform for Grandstream access points. Secure networks can be deployed in seconds using GDMS mobile app or the web browser interface. Keep an eye on the network’s performance with real-time monitoring, alerts, statistics and more.

GWN Manager
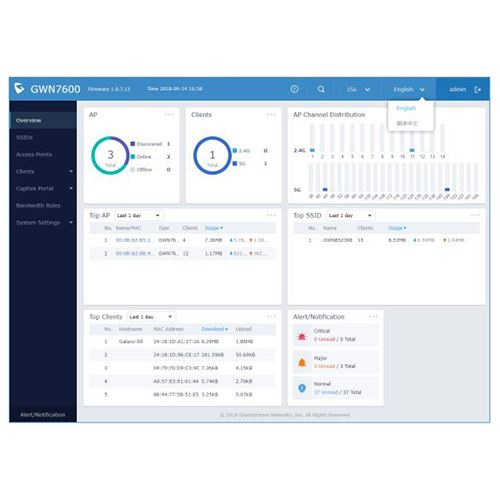
GWN Manager is a on-premise enterprise- grade, management platform for an unlimited number of Grandstream access points. Typically deployed on a customer’s private network it offers simplified configuration and management, real-time monitoring, alerts, statistics and more.
Embedded Controller
Grandstream's GWN series of Routers and APs includes controller software at no extra cost and it is simply built-in to the product’s web user interface. Our embedded controllers can auto discovery and auto-provision any in-network GWN series AP from the designated Provisioning Master, which also offers a centralized provisioning and management interface.
Security Features
Like any technology, Wi-Fi has its own share of security concerns. The nature of any wireless network allows anyone with malicious intent to locate themselves close to an access point in order to infiltrate a network. More than 80 percent of U.S. companies have been successfully hacked, according to a Duke University/CFO Magazine Global Business Outlook Survey. Being that a Wi-Fi attack can occur in only 2 seconds, we set out to create our networking products to solve many traditional Wi-Fi security problems by building a variety of high-end security protections into the Networking Management platforms.
Access helpful technical documentation and how-to guides about our products by visiting the Documentation Center HERE.
Infrastructure Security
Network Security: We use cybersecurity and surveillance technology to provide multiple layers of protection and defense.
Deployment Security: Each of our service systems and programs has an independent account with corresponding permissions to manage the deployment
DDoS Protection: Our server will automatically detect abnormal massive data outflow and shield abnormal data to prevent it from being used by DDoS attacks.
Authentication Security
User Authentication: Users must use their own accounts and passwords to log in to the GDMS Networking. Users are required to provide additional information based on risk factors.
Multi-factor Authentication: In addition to the password, we also provide multi-factor authentication, additional security hardening account. This can greatly reduce the risk of unauthorized access if a user’s password is accidentally disclosed.
Data Security
Transmission Encryption: All customer data transmitted to our servers over public networks is protected using strong encryption protocols.
Data Storage and Encryption: Consumer data stored the data base is encrypted to ensure confidentiality and integrity.
Data Access Permissions and Restrictions: The data stored in our system is owned by the user, and the user configures role permissions to control access restrictions.
Invalid Data Disposal: When a user deletes data such as a device or template, the associated data is deleted immediately.
Legal Basis for Data Processing: GDMS Networking is GDPR compliant, and data stored in its US and EU servers are managed separately.
Operation Security
Record and Monitor: We provide 24/7 operation and maintenance support. We monitor the real-time CPU/ memory/hard disk/network status of all servers, and have separate monitoring and abnormal alarm for each service.
Vulnerability Management: We conduct regular internal penetration test and security inspection, including common Web attack test, business logic and permission test, software reinforcement for public vulnerabilities, and etc. Once we find a vulnerability that needs to be fixed, we will immediately track it until it is resolved through a patch.
Backup: We carry out incremental backup every day and full database backup every week, and back up data to Amazon S3 for encrypted storage, to ensure that user data will not be lost.
Business Continuity Assurance: All servers have the hot backup and automatic migration functions. If some servers are abnormal, they can be automatically switched over to normal nodes to ensure uninterrupted service running.
Featured Highlights
GDMS Networking Tutorial Videos
YouTube Playlist
In this playlist you'll find a collection of technical videos regarding GDMS Networking platform
Learn More
How to Use Grandstream Device Management System
Blog Post
Grandstream Device Management System (GDMS) empowers installers with a cloud-based solution to easily manage all of their Grandstream unified communications and networking deployments before, during, and after the project. Recently, GWN.Cloud was integrated into GDMS, enabling users to manage a complete Grandstream portfolio deployment from one account.
Learn More



























.webp?width=250&height=131&name=how-to-use-gdms-q1-2024%20(1).webp)